This article has been updated to add some vCenter Role Assignment recommendations as of March 11th, 2011. Recently, I was having a conversation about the need for some domain service acocunts to support vCloud installations and I realized there is not a great grouping of which applications need what service accounts and how they map to usage. So here is a little bit of insight on what I have seen in the field and actually how I setup the service accounts in my lab and over the past couple months as it relates to VMware vCloud specifically. It is important to understand that by using service accounts you can control in a single place the access by certain services within vCloud Director as things change over time. Personally I am a big fan of service accounts and I think the more you have specific to a particular set of services the better it is and the easier you can audit access.
VMware vSphere vCenter Service Account:
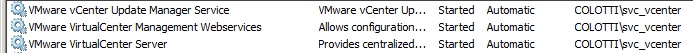
Usage – This service account is sometimes used by folks to run the vCenter services and can also be used to install the vCenter services.
Requirements – Allow “Log on as a Service” right and Local administrator to perform installation. Also post install the service account will need to be set on the Update Manager Service. By default it is setup as ‘SYSTEM’ and startup of the service will most likely fail.
Database Access – DBO on vCenter Database and Update Manager Database.
vCenter Role Assignment – Generally I assign this as a top level Administrator and I also use this as the account to add plugins and other admin related items to vCenter
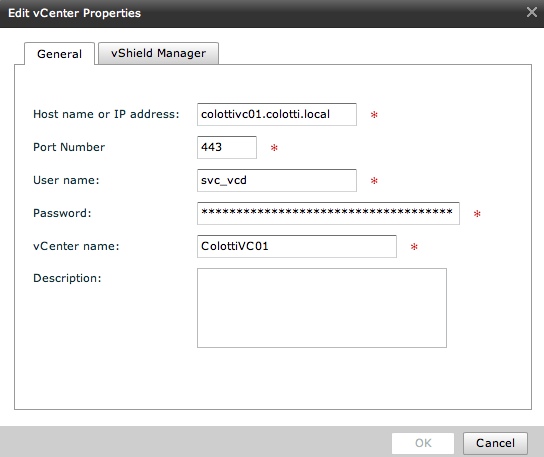
VMware vCloud Director Service Account:
Usage – This service account is used only INSIDE vCenter assigned to a copy of the Administrator role for vCloud Director to connect to vCenter to perform operations. This is also used to deploy vShield Edge Devices from inside vCloud Director
Requirements – No Specific ones
Database Access – none this is not used to connect to any DB’s only to vCenter
vCenter Role Assignment – This also needs to be assigned at the top most level of vCenter as an Administrator I recommend making a copy of the Administrator Role to a new one so in the future this role could possibly be limited for security purposes.
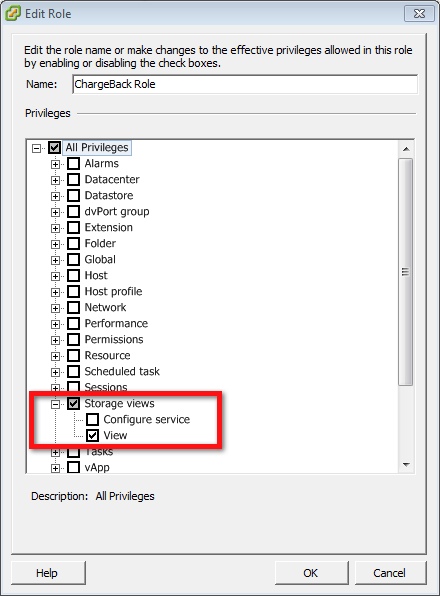
VMware Chargeback Service Account:
Usage – This service account is used for multiple things actually. It is used to run the Chargeback services, connect to the vCenter, as well as connect to the vCenter Database. It is the most used service account and has specific rights requirements
Requirements – Allow “Log on as a Service” right and Local administrator to perform installation. By default the services will be set to run as the context of the user logged in during the installation so BE SURE to log in as this service account to perform the Chargeback install.
Database Access – Read Only access to the vCenter Database, DBO of the Chargeback database
vCenter Role Assignment – This requires “Read Only PLUS Storage Views” access in vCenter for NORMAL operations. This should be a new role in vCenter you create and assign to this service account and also should be applied at the top most level down. NOTE: During installation and plugin registration this service account does need to be flipped to Administrator.

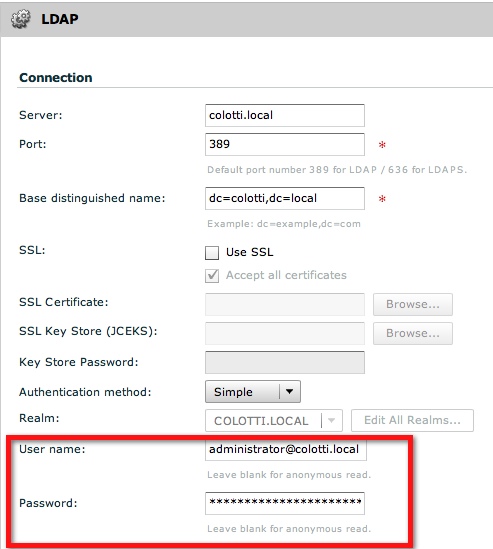
LDAP Service Account:
Usage – This service account is used to connect vCD to LDAP for user lookups and importing users from LDAP. In some cases this can be the same as the vCloud Director service account that interacts with vCenter, but that is up to you. Most customers want a dedicated LDAP service account so they can audit Active Directory or LDAP
Requirements – Read Access to LDAP or AD as well as join domain access if you plan on joining domains with Guest Customization
Database Access – None it does not interact with any Databases except LDAP
vCenter Role Assignment – None required.
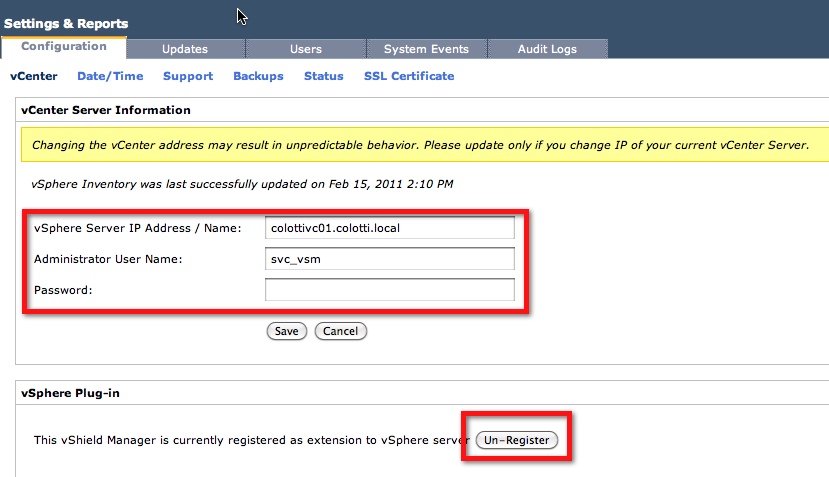
vShield Service Account:
Usage – This information will be pre-populated by vCloud Director with version 5.0. Changing this is not recommended as it will simply change back at some point. This may be modified at some point for proper auditing and it could be changed at a later date.
Requirements – No specific requirements
Database Access – None it does not interact with any Databases
vCenter Role Assignment – Like most of the other service accounts this requires top down vCenter Administrator access due to the nature of what it must talk to, but it will be the same account as vCloud Director is using to connect to vCenter so rights should already be assigned.
Hopefully this provides some insight as to the service accounts you may want to setup prior to installing and configuring VMware vCloud Director. As new products like Request Manager are introduced, these in turn will most likely use additional service accounts especially within vCenter to control access to certain functions. Service accounts have always been a useful tool, but in many POC’s we see folks using their own personal credentials or other known accounts causing problems later when passwords change. Sometimes we forget which account we created so setting these up in the beginning can save you some headache.
Summary (Updated 7-23-11):
Below is a simple table as a basic cross reference for the accounts discussed above. It should be noted that having these up front will make it easier for proper security and troubleshooting down the line.
|
Access Required |
Components that require Domain Service Accounts |
||||
|
vCloud Director |
vCloud Connector |
vCenter and Update Manager |
vCenter ChargeBack |
vShield Manager |
|
| vCenter Role |
Admin |
Admin |
N/A |
Read Only Plus Storage Views |
Admin |
| Local System Access |
N/A |
N/A |
Log on as a Service |
Log on as a Service |
N/A |
| AD / LDAP Access |
Read Only Access to AD |
N/A |
N/A |
Read Only Access to AD |
N/A |
| vCenter Database |
N/A |
N/A |
DBO |
Read Only |
N/A |
| vCloud Database |
RESOURCE, DBA, |
N/A |
N/A |
Read Only |
N/A |
 Chris Colotti's Blog Thoughts and Theories About…
Chris Colotti's Blog Thoughts and Theories About…

Great post! Thanks for combining and sharing this useful info.