My vShield App Firewall Use Case
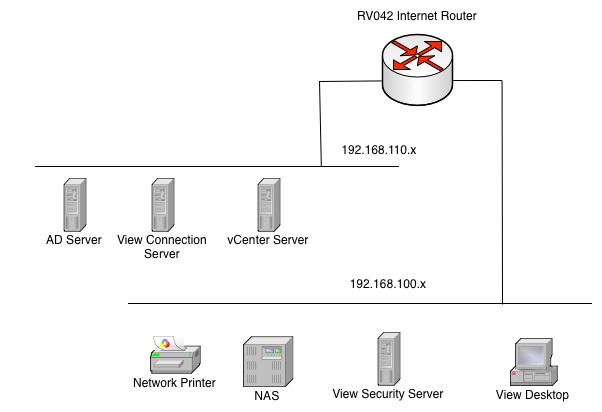
The scenario for why I wanted to try and use the vShield App Firewall was pretty basic and is probably similar for most folks. Everything in the “Lab” space is virtual except for some of the storage devices and all of the personal devices. However I have the networking split between two subnets
- 192.168.100.x – All Physical and Personal Devices
- 192.168.110.x – Most Virtual Machines
When I decided to build the home lab I wanted to have some level of remote access using VMware View. Now I have pretty limited View expertise, just enough to get it setup and working, but because of my home router I have a challenge. The home router will only do Port Forwarding to local IP addresses, and that router is part of the 192.168.100.x network. Therefore my View Security Server needed to have an IP address on that network, making it part of my “trusted” network while all the other virtual machines are in the lab network. Even though I am only passing Port 443 that Virtual Machine was still going to be part of my trusted LAN. So I decided to have some fun with the vShield App Firewall. The diagram below show some of the network layout. You can see since the View Security Server is on a trusted network.
How vShield App Firewall Helped
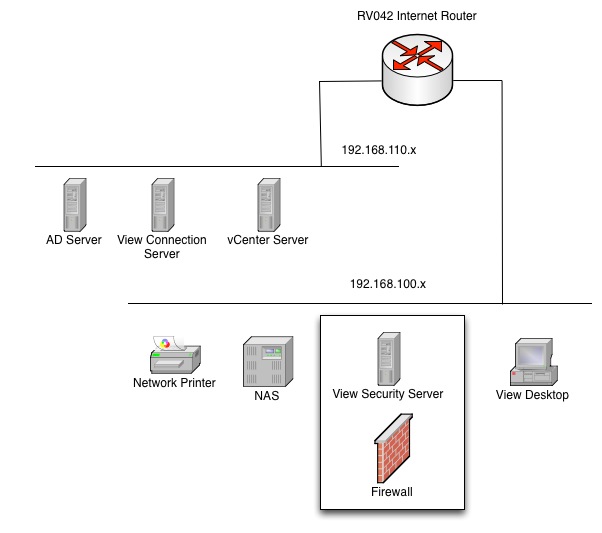
My goal ultimately was to allow internet traffic on port 443 and PCoIP into the virtual machine for View Security Server, but then limit that virtual machine’s ability to communicate to other things on the trusted network. Effectively I wanted to put a DMZ around the virtual machine. This is why vShield App Firewall is so high on the cool scale, it does exactly that! The goal is to basically change the diagram to look like below where the View Security Server is boxed into a DMZ even though it is on the same subnet
I would like to point out that the View Security Server is NOT part of the Active Directory Domain, and is a workgroup machine only with local credentials. Therefore my only concern was making sure I could block access to the other IP addresses on the trusted LAN.
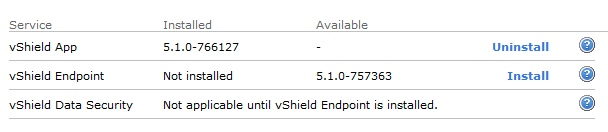
Installing and Configuring vShield App Firewall
First thing you need to do is obviously license and install the vShield Cloud Network Security suite, (vCNS), and then install the vShield App Service on all the hosts in the cluster. The latest versions are very good about not locking you out of vShield Manager and vCenter Server once they are enabled. You can see the screen shot below that the option is enabled. The install is pretty self-explanatory and you will end up with a vShield Firewall Appliance per ESXi Host.
vShield App Firewall Rules
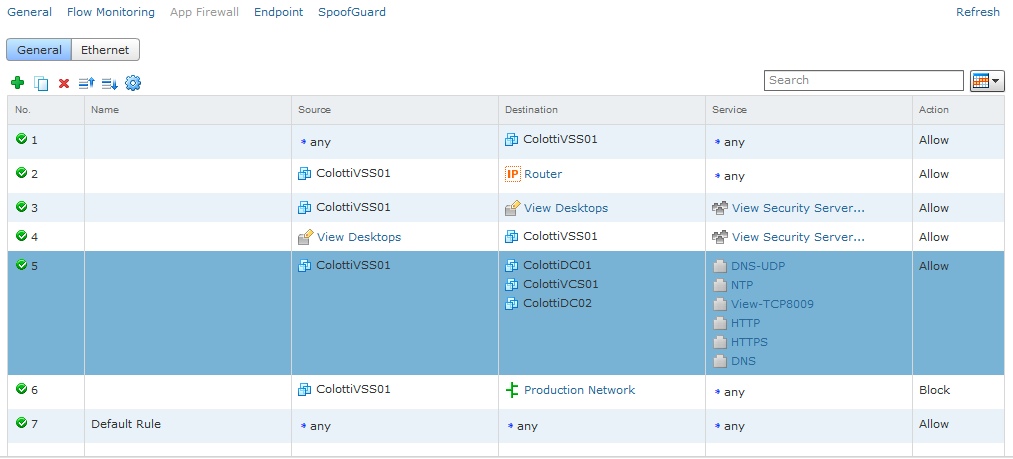
Now for those that never wrote firewall rules this is where worlds can collide a bit. Personally back in my system admin life I was also a Checkpoint Firewall administrator so I have always had a good understanding of source, destination, services, etc. The new vShield App Firewall rules look very similar to other enterprise firewalls. The exception is you can write rules by specific virtual machine as well as services, and defining networks. You also get access to flow information so see blocked and accepted flows to easily help you troubleshoot.
Because I wanted to allow access to this View Security Server, but deny access from that virtual machine to much of the other network below is the current rule set I have been playing with. It still needs some tuning as there is still technically a few holes.
However it is functional and has provided me what I wanted. The virtual machine, although on the same network, cannot talk to anything on that network and is only allowed to reach AD, DNS, View Connection server, and the View Desktops. I can certainly refine the rules further, but for the initial use case it is working and I cannot get to anything from the View Security Server except the internet and the view connections are working to the desktops. Many of the custom service rules I had to pull from the View Firewall Documentation.
Final Thoughts on the vShield App Firewall
I think this product is VERY high on the cool scale. I know at VMworld we asked people if they thought it was cool and lots of people raised their hands. When we followed up with “who is using it?”, most of the hands went down. So even though this is a single and isolated use case it proves the use case and I would encourage you to try it. Just don’t get too frustrated if things get too locked down. Use the Flow Monitoring to see what is going on and keep adjusting the rules. Make sure you have the ports you need for that service, but you can now isolate a single, or group of virtual machines in a DMZ without ever using a real hardware firewall! It goes without saying that this can be done for things outside a lab as well.
 Chris Colotti's Blog Thoughts and Theories About…
Chris Colotti's Blog Thoughts and Theories About…


Chris is if I installed the vcns in. How do I enable or as you put it install the vshield app appliance for the host. Is that done from vShield Manager or from vCenter?
You have to install app firewall from vcenter to enable it.