I have been running a cloud based version of the Ubiquiti Unifi Controller for just about a year now. I decided to run it this way because I happen to manage my home office gear as well as a small setup for my church and a local RV park. The cloud based controller version was a perfect solution do have all the sites under one roof. However, it does cost money to host it every month, and there is some management of the virtual server, but all in all it’s been flawless. It also gives every device the same place to call home and has always stayed online. Last week I also blogged about how the Unifi iOS app can connect to that controller and I also have access to all those sites on a mobile device. What some people don’t know yet is Ubiquiti also fired up a cloud aggregation portal that they host and you can register multiple controllers with. That got me thinking, should I break the sites out into individual controllers using the new Unifi Cloud Key? Well first I needed to see what this little device was all about.
Unifi Cloud Key Architecture
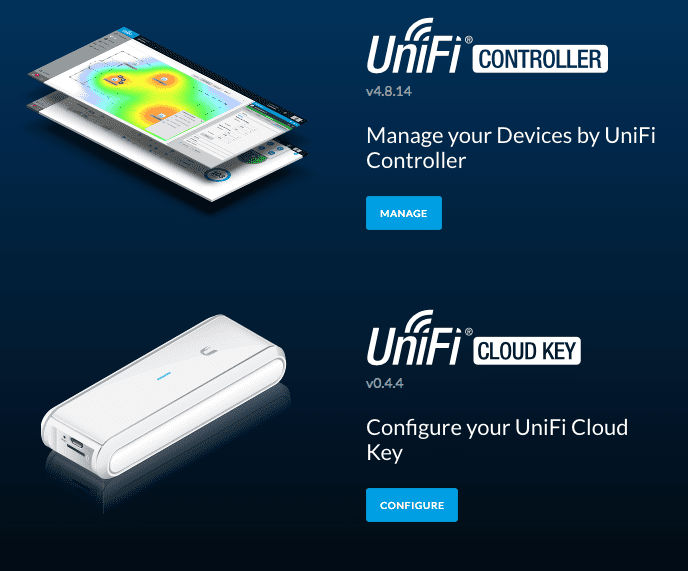
Right off the bat when you plug this it and power it up with PoE, it will try to use DHCP to get online. Once you know the IP address and connect to it one thing jumps right out. There is TWO management interfaces on the single IP address. The first is to the Unifi Controller installation, the other is to manage the Unifi Cloud Key firmware itself.
What you will find is that both interfaces are on HTTPS and they are separated in the following manner:
- https://<Cloud_Key_IP>/ = Start Screen
- https://<Cloud_Key_IP>/Login = Unifi Cloud Key Login
- https://<Cloud_Key_IP>:8443/ = Unifi Controller Login
This means that most likely you cannot change the controller’s startup to use port 443 like many people do with a cloud based controller since 443 is already in use for the Key management. That’s okay for the most part if you ask me. My public cloud controller I did switch to 443 on the port to make it easier to remember. The point here on the architecture is that it’s two web services on the same device using different ports. It also appears that non SSL is forced to SSL for the login pages.
There is a microSD that comes with it that the manual says is used for backup, but so far I have not found any way to utilize it. The forums indicate it’s for future use while the setup doc says “To back up the Unifi Controller database and configuration, use the included microSD Card
Configuring the Unifi Cloud Key
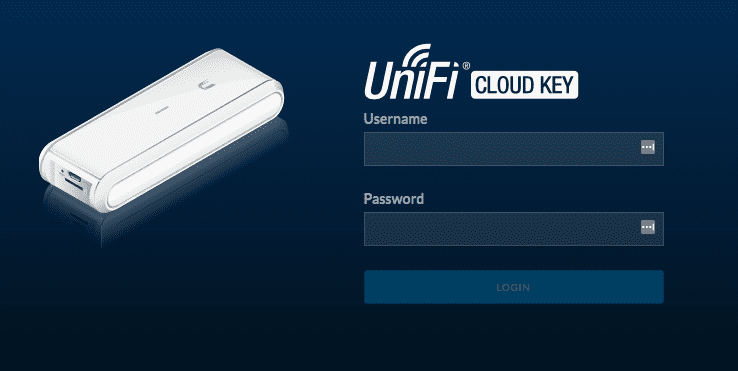
This is pretty straight forward and only a few things to look at. Once you click “Configure” under Configure Your Cloud Key on the start page you will get the key login.
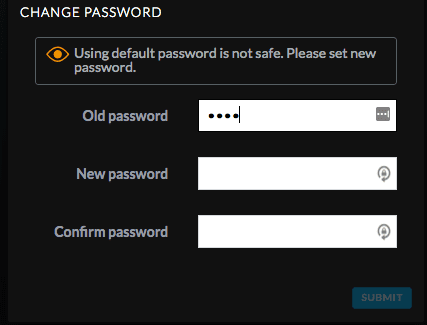
Once logged in the first thing it’s smart enough to make you do is change the default password.
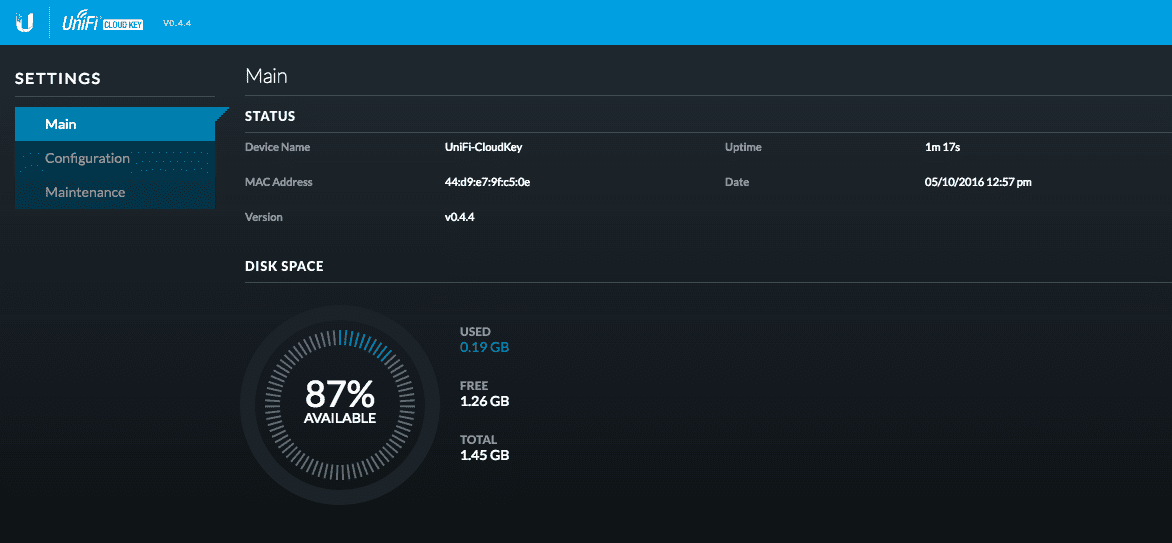
Once you get connected you are presented with a dashboard and a few links. You can see there is on;y 1.45 GB available showing…so again not sure where the MicroSD is accounted for and how you access it for backups.
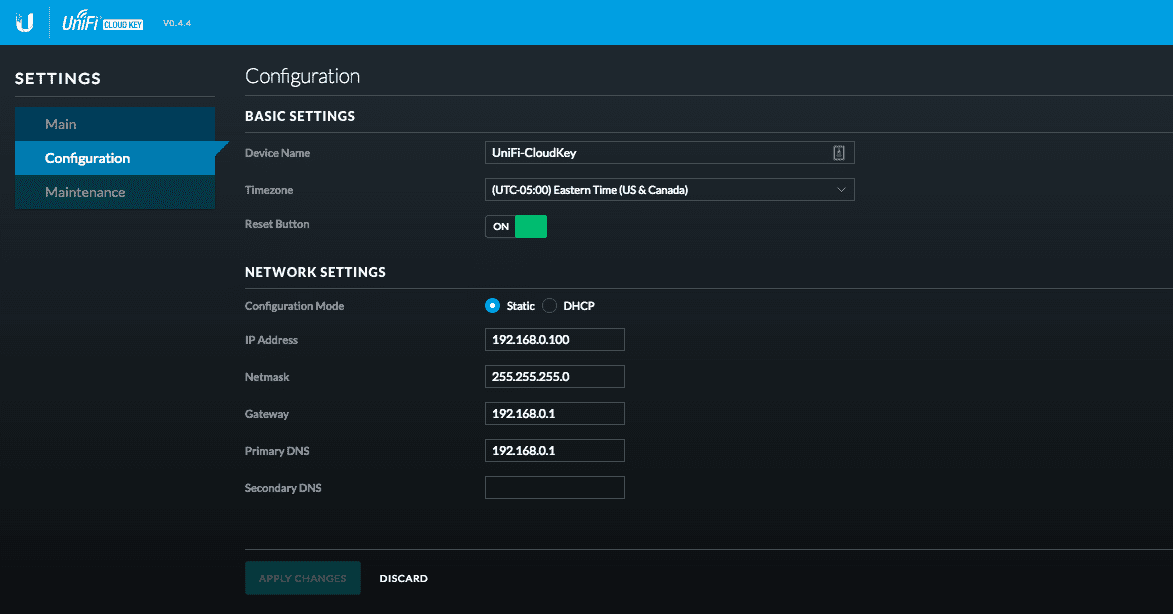
Under Configuration you can set the device name, time zone, and IP address of the device itself. It’s by default set to DHCP and also has a fallback IP address if no DHCP can be reached.
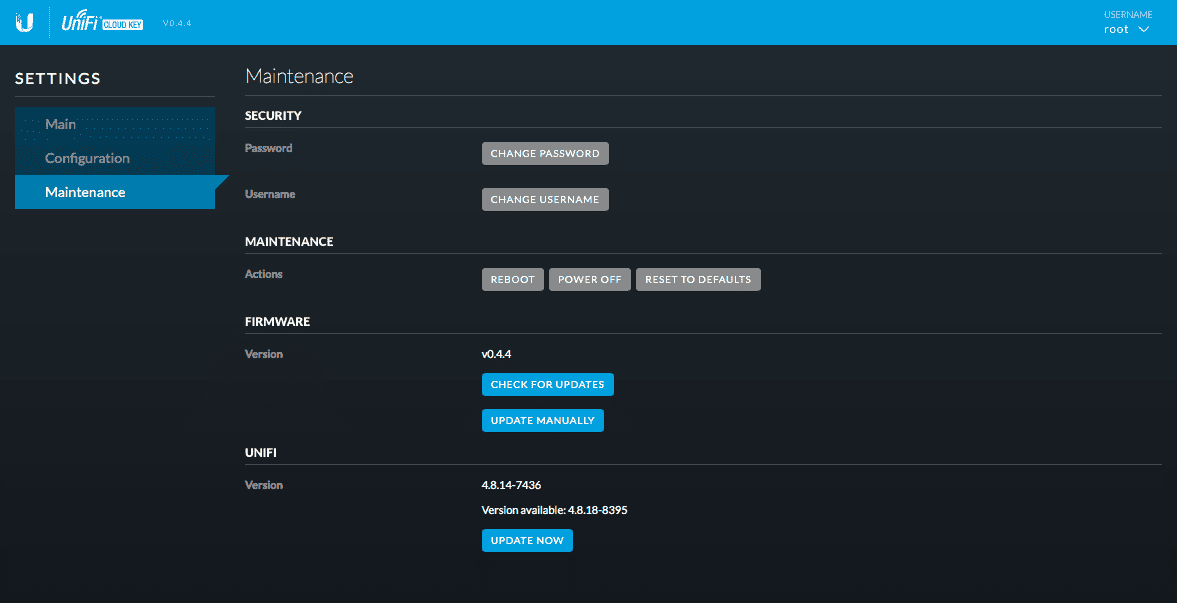
Lastly under Maintenance you can change the password, default username, reboot, shutdown, reset to defaults, and check for updates for the Key Firmware and the Unifi Controller software
NOTE: I have found that if you update the Unifi Controller version then reset the device back to factory settings, the Unifi version goes back to whatever was loaded on it when you obtained it. I have posted this on the Ubiquiti Forums to see why that is.
UPDATED 5/11/16: This is the expected behavior with a major Cloud Key firmware upgrade. That will always ship with a new “lowest” default version so in this case 4.8.14 is the lowest it will always revert back to on reset to defaults.
Once you’ve completed this setup you can access the Unifi Controller and configure it same as you do any other version of the controller software. For the sake of brevity I will not cover that process as it’s very simple.
Initial Unifi Cloud Key Pros
All in all the Unifi Cloud Key out of the box is pretty sweet.
- Easy to set up
- Great price point for a 1:1 site:key setup on small installations
- Form factor and PoE connectivity is great
- iOS app can reach it as long as on local LAN
- Federated cloud access using the Ubiquiti Cloud (Future blog post)
Initial Unifi Cloud Key Cons
There are a few things I started to wonder as I was playing with it, at least specific to my environment compared to the cloud based controller
- Access via IP not DNS (I don’t have a local DNS server….YET until the USG support static DNS entries via UI without JSON files)
- Have to keep the ports pre-configured due to split web services
- Can only manage via WebRTC currently from Android not iOS via UBNT Cloud
 Chris Colotti's Blog Thoughts and Theories About…
Chris Colotti's Blog Thoughts and Theories About…



Nice review. I am wondering if it’s a good idea to buy a cloud key for a site where there is no computer to use for the “standard” contoller software. I am interested in a solution that can simply replace a local computer with the controller software on it. I am not interested in cloud (remote) management, and to be honest I really DON’T want to depend on a cloud service to run my network. I want a solution that works completely by itself. Can you please tell me if this cloud key can run by itself, without any cloud service?
Thanks
Fabio Muzzi
I’d say that’s exactly what the key is intended for. The cloud access to it is free and enables secure remote management of it so I’d still recommend it.
Thanks Chris, you have been far more clear than the brochures on UBNT web site.
I am new to all this stuff and this has to be one of the worst vendor documented/explained solutions I have ever come across. thanks for making it a bit clearer.
They have their documentation challenges, but then again so do most vendors. Once you get it running it is one of the easiest products to use and it’s pretty hands off at that point. I am actually still running a cloud key today. I have thought about switching to a cloud VPS or local Docker Container as well.